- Cisco Asa Anyconnect Vpn Configuration
- Cisco Anyconnect Route Details
- Cisco Asa Ssl Vpn Configuration
- Cisco Asa Vpn Client Download
- Cisco Asa Vpn Client License
- Cisco Asa Vpn Client Windows 10
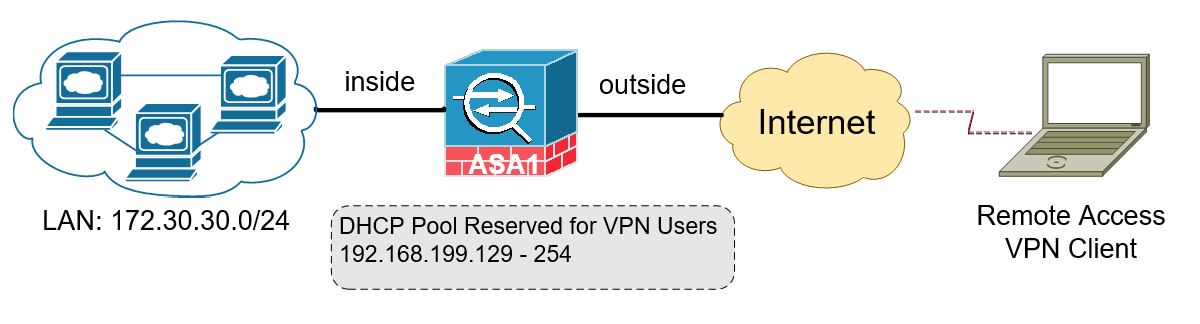
Thanks to technology in today’s world many people have the luxury of working remote. Today we will discuss configuring a Cisco ASA 5506-X for Client Remote Access VPN. Below is the copy and paste config
Copy and paste config
SRG-ASA# show run
ASA Version 9.4(1)
ip local pool VPN_Pool 192.168.1.100-192.168.1.120 mask 255.255.255.0
!
interface GigabitEthernet1/2
nameif inside
security-level 100
ip address 192.168.0.1 255.255.255.0
!
access-list split standard permit 192.168.0.0 255.255.255.0
access-list ra-split standard permit 192.168.0.0 255.255.255.0
access-list ra-split-nonat extended permit ip 192.168.0.0 255.255.255.0 192.168.1.0 255.255.255.0
user-identity default-domain LOCAL
aaa authentication ssh console LOCAL
no snmp-server location
no snmp-server contact
sysopt connection tcpmss 1387
crypto ipsec ikev1 transform-set ESP-3DES-MD5 esp-3des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-DES-SHA esp-des esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-DES-MD5 esp-des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-SHA esp-aes esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-MD5 esp-aes esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
crypto ipsec ikev1 transform-set myset esp-3des esp-sha-hmac
crypto ipsec ikev1 transform-set myset mode transport
crypto ipsec ikev1 transform-set L2TP-tunnel esp-3des esp-sha-hmac
crypto ipsec ikev1 transform-set L2TP-tunnel mode transport
crypto ipsec ikev1 transform-set ESP-AES-128-SHA-TRANS esp-aes esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-SHA-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-AES-128-MD5-TRANS esp-aes esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-128-MD5-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-AES-192-SHA-TRANS esp-aes-192 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-SHA-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-AES-192-MD5-TRANS esp-aes-192 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-192-MD5-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-AES-256-SHA-TRANS esp-aes-256 esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-SHA-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-AES-256-MD5-TRANS esp-aes-256 esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-AES-256-MD5-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-3DES-SHA-TRANS esp-3des esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-3DES-SHA-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-3DES-MD5-TRANS esp-3des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-3DES-MD5-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-DES-SHA-TRANS esp-des esp-sha-hmac
crypto ipsec ikev1 transform-set ESP-DES-SHA-TRANS mode transport
crypto ipsec ikev1 transform-set ESP-DES-MD5-TRANS esp-des esp-md5-hmac
crypto ipsec ikev1 transform-set ESP-DES-MD5-TRANS mode transport
crypto ipsec ikev1 transform-set transform-amzn esp-aes esp-sha-hmac
crypto ipsec ikev2 ipsec-proposal DES
protocol esp encryption des
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal 3DES
protocol esp encryption 3des
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES
protocol esp encryption aes
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES192
protocol esp encryption aes-192
protocol esp integrity sha-1 md5
crypto ipsec ikev2 ipsec-proposal AES256
protocol esp encryption aes-256
protocol esp integrity sha-1 md5
crypto ipsec security-association lifetime seconds 3600
crypto ipsec security-association replay window-size 128
crypto ipsec security-association pmtu-aging infinite
crypto ipsec df-bit clear-df outside
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65533 set ikev1 transform-set L2TP-tunnel ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA ESP-3DES-MD5 ESP-DES-SHA ESP-DES-MD5
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65534 set ikev1 transform-set myset ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA ESP-3DES-MD5 ESP-DES-SHA ESP-DES-MD5
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set pfs
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set ikev1 transform-set ESP-AES-128-SHA ESP-AES-128-MD5 ESP-AES-192-SHA ESP-AES-192-MD5 ESP-AES-256-SHA ESP-AES-256-MD5 ESP-3DES-SHA ESP-3DES-MD5 ESP-DES-SHA ESP-DES-MD5 myset
crypto dynamic-map SYSTEM_DEFAULT_CRYPTO_MAP 65535 set ikev2 ipsec-proposal AES256 AES192 AES 3DES DES
crypto map SRG_VPN 64553 ipsec-isakmp dynamic SYSTEM_DEFAULT_CRYPTO_MAP
crypto map SRG_VPN interface outside
crypto ca trustpool policy
crypto isakmp identity address
crypto ikev2 policy 1
encryption aes-256
integrity sha
group 2
prf sha
lifetime seconds 28800
crypto ikev2 policy 2
encryption aes-256
integrity sha256
group 2
prf sha
lifetime seconds 28800
crypto ikev2 policy 3
encryption aes-256
integrity sha
group 2
prf sha256
lifetime seconds 28800
crypto ikev2 policy 5
encryption aes-256
integrity sha256
group 2
prf sha256
lifetime seconds 28800
crypto ikev2 policy 10
encryption aes-192
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 20
encryption aes
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 30
encryption 3des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 policy 40
encryption des
integrity sha
group 5 2
prf sha
lifetime seconds 86400
crypto ikev2 enable outside
crypto ikev2 enable inside
crypto ikev1 enable outside
crypto ikev1 enable inside
crypto ikev1 policy 1
authentication pre-share
encryption 3des
hash md5
group 2
lifetime 86400
crypto ikev1 policy 2
authentication pre-share
encryption aes-256
hash sha
group 2
lifetime 28800
crypto ikev1 policy 5
authentication pre-share
encryption aes-192
hash sha
group 2
lifetime 28800
crypto ikev1 policy 10
authentication pre-share
encryption aes
hash sha
group 2
lifetime 86400
crypto ikev1 policy 20
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto ikev1 policy 200
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 28800
crypto ikev1 policy 201
authentication pre-share
encryption aes
hash sha
group 2
lifetime 28800
!
dhcpd address 192.168.0.100-192.168.0.200 inside
dhcpd domain surge.local interface inside
dhcpd update dns interface inside
dhcpd enable inside
!
username jgranados password zI/d0As121029oXGg encrypted privilege 15
username jgranados attributes (<–Shouldn’t need attributes but doesn’t hurt to add)
vpn-group-policy DfltGrpPolicy
!
group-policy DfltGrpPolicy attributes
dns-server value 8.8.8.8 8.8.4.4
vpn-tunnel-protocol ikev1 l2tp-ipsec ssl-client ssl-clientless
ipsec-udp enable
split-tunnel-policy tunnelspecified
split-tunnel-network-list value ra-split ( group-policy filter internal
dynamic-access-policy-record DfltAccessPolicy
tunnel-group DefaultRAGroup general-attributes
address-pool VPN_Pool
tunnel-group DefaultRAGroup ipsec-attributes
ikev1 pre-shared-key SECRET
tunnel-group DefaultRAGroup ppp-attributes
authentication ms-chap-v2
SRG-ASA#
Cisco Asa Anyconnect Vpn Configuration
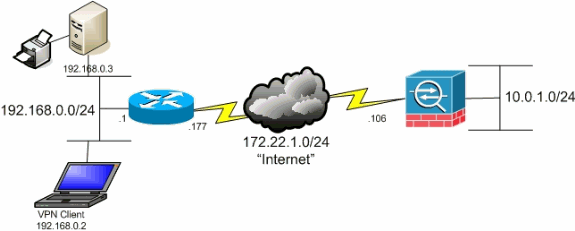
Comment and share: Quick guide: AnyConnect Client VPN on Cisco ASA 5505 By Lauren Malhoit Lauren Malhoit has been in the IT field for over 10 years and has acquired several data center certifications. Both IPSec VPNs and SSL VPNs are supported by Cisco ASA 5500 firewalls. The newest generation of remote access VPNs is offered from Cisco AnyConnect SSL VPN client. This is supported by Cisco ASA 8.x. The AnyConnect SSL VPN provides the best features from.
Configuring MAC VPN Client
Cisco Anyconnect Route Details
Many users are now using MAC clients. Below you will find step by step instructions on configuring a MAC Client for VPN Remote Access.
Cisco Asa Ssl Vpn Configuration
1. Open “System Preferences” and go to “Network”. Choose the add setting highlighted below, then select VPN.
2. Configure the following VPN interface with the following settings
INTERFACE: VPN
VPN TYPE: CISCO IPSEC
SERVICE NAME: (Preferably Company Name or Easy to Remember Description)
Cisco Asa Vpn Client Download
3. Select “Authentication Settings” and type your as the shared secret. Leave group name empty and choose ok.
Cisco Asa Vpn Client License
4. Input you outside interface IP address as the server address, or if you’ve created a DNS entry you can also use that. You can also select “Show VPN status in the menu bar” which makes it a lot easier to connect in the future. Then Connect.
Cisco Asa Vpn Client Windows 10
5. After Connecting the SURGE connection will show green like this.
